Introduction
The 21st Century Cures Act didn't just suggest interoperability—it mandated it. Healthcare organizations are now expected to securely share patient data across applications, platforms, and ecosystems. SMART on FHIR is the framework making that mandate a reality.
SMART on FHIR is a framework that combines FHIR APIs with OAuth 2.0 and OpenID Connect to enable secure, standardized access to electronic health records (EHRs). It allows developers to build interoperable healthcare apps that integrate seamlessly with systems like Epic and Cerner.
In this guide, you'll learn what SMART on FHIR is, how it works step-by-step, its architecture, real-world use cases, and how developers can build and secure SMART-enabled applications.
What Is SMART on FHIR?
SMART on FHIR is an interoperability standard that layers secure OAuth 2.0 and OpenID Connect authorization on top of the FHIR protocol, allowing third-party apps to safely access EHR data through standardized APIs. It enables portable, reusable healthcare apps that work across different systems without custom integrations.
In a nutshell, SMART FHIR helps to view the intersection of two major healthcare innovations: data interoperability and secure access control. SMART stands for Substitutable Medical Applications and Reusable Technologies.
When paired with FHIR technology, it creates an open framework that enables apps to securely access patient data stored in electronic health records (EHRs) via standardized API calls.
SMART on FHIR transforms healthcare APIs into secure, app-ready platforms using OAuth 2.0 and OpenID Connect.
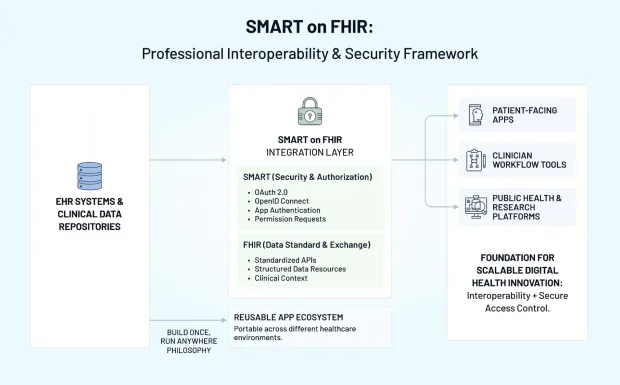
While FHIR defines how data is structured and exchanged, SMART defines how apps authenticate, request permissions, and receive clinical context. This combination makes SMART on FHIR the glue that holds modern healthcare app ecosystems together.
SMART on FHIR is designed to be reusable. A developer can build a SMART on FHIR app once and deploy it in multiple healthcare environments without rebuilding the integration each time. This “build once, run anywhere” philosophy dramatically reduces integration friction and enables a thriving marketplace of apps that serve clinicians, patients, payers, and public health agencies.
From a conceptual standpoint, Smart FHIR represents a shift from closed platforms to a more open, modular ecosystem—one where software innovation is encouraged rather than restricted.
As your understanding deepens, SMART on FHIR becomes more than just a technical specification it’s a foundation for scalable digital health innovation, patient empowerment, and consistent security across diverse healthcare systems.
FHIR vs SMART on FHIR: What’s the Difference?
While often used together, FHIR and SMART on FHIR serve different purposes.
| Feature | FHIR | SMART on FHIR |
|---|---|---|
| Definition | Data standard for healthcare interoperability | Security + app framework built on FHIR |
| Purpose | Defines how healthcare data is structured and exchanged | Enables secure app access to FHIR APIs |
| Authentication | Not included, but expects a security layer | Uses OAuth 2.0 and OpenID Connect |
| Focus | Data format and APIs | Authorization and app integration |
| Use Case | Data exchange between systems | Building third-party healthcare apps |
In simple terms, FHIR defines how data is structured, while SMART on FHIR defines how apps securely access that data.
SMART on FHIR vs Other Healthcare Integration Approaches
| Approach | Description | Limitation |
|---|---|---|
| HL7 v2 | Legacy messaging standard | Limited interoperability |
| FHIR | Modern API-based data exchange | No built-in security layer |
| SMART on FHIR | Secure app framework on FHIR | Requires proper OAuth setup |
SMART on FHIR bridges the gap between data interoperability and secure access control.
FHIR Technology and the FHIR Protocol
If SMART on FHIR is the engine for app interoperability, then FHIR technology is the fuel. FHIR—Fast Healthcare Interoperability Resources—introduced a modern, web-friendly approach to representing and retrieving healthcare data.
It uses REST APIs, JSON or XML formats, and well-defined resource models for entities like Patient, Observation, Encounter, Condition, or MedicationRequest. The FHIR protocol outlines how systems search, read, write, and interact with these resources, creating predictable patterns that every SMART on FHIR app depends on.
Before FHIR, integrating systems required custom HL7 messaging, proprietary interfaces, or manual exports. FHIR technology changed that by adopting industry standards used in mainstream software development. The result is an API-driven environment that makes health data far more accessible and easier to integrate.
But the FHIR protocol alone doesn’t solve authentication, user identity, permissions, or authorization. That’s where SMART comes in. The SMART layer sits on top of FHIR, defining how apps should authenticate using OAuth 2.0, request scopes, and receive information about which patient chart or clinical encounter is active.
Together, SMART on FHIR and the underlying FHIR protocol create a complete framework that supports secure, context-aware health data exchange.
FHIR defines the data. SMART on FHIR defines how applications securely access it.
How SMART on FHIR Works
SMART on FHIR works by combining FHIR APIs with OAuth 2.0 and OpenID Connect to create a secure, standardized way for apps to access EHR data. An app discovers the FHIR server’s capabilities, redirects the user for authentication, receives an access token with SMART scopes, and then uses that token to call FHIR resources with patient or encounter context.
Although SMART on FHIR includes multiple layers, the way it operates is surprisingly intuitive once broken down. At the highest level, SMART on FHIR establishes a secure handshake between three actors: the application, the FHIR server, and the authorization server.
The process begins when a SMART on FHIR app queries the FHIR server’s well-known metadata endpoint. This endpoint provides critical information such as OAuth URLs, supported SMART scopes, launch parameters, token formats, and available API capabilities.
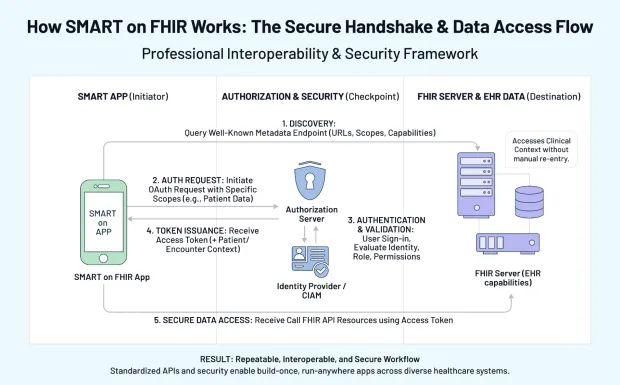
Once the app understands the server’s configuration, it initiates an OAuth authorization request asking for access to specific FHIR resources. This request includes scopes that define what the app wants to read or write—such as patient data, clinical observations, or medications.
When the user signs in typically through the healthcare organization’s identity provider or a CIAM platform the authorization server evaluates their identity, role, permissions, and the app’s requested scopes. Only after validating all of this does it issue an access token and optionally an ID token.
The SMART on FHIR app then uses the access token to make secure calls to the FHIR protocol endpoints. Because the token includes patient or encounter context (when applicable), the app opens directly in the correct segment of the clinician or patient workflow. This context ensures efficiency and removes the need for repeated navigation or manual data entry.
Together, these steps create a repeatable, interoperable, and secure workflow. By standardizing how apps launch, authenticate, authorize, and access data, SMART on FHIR enables developers to build reusable apps that work across any SMART-enabled FHIR server with minimal customization driving large-scale interoperability and better digital health experiences.
Components of SMART on FHIR
The SMART on FHIR ecosystem is built around three tightly integrated components that work together to support secure, standards-based healthcare app functionality.
The first layer is FHIR technology, which defines the data structure and interaction rules. This ensures that SMART on FHIR apps can reliably request and interpret patient data using the FHIR protocol. Without this uniform data standard, interoperability would collapse under inconsistent schemas and incompatible formats.
The second layer is the security framework. SMART leverages OAuth 2.0 and OpenID Connect to authenticate users and authorize apps. This allows precise control over who can access which FHIR resources. SMART-specific scopes—such as patient/Observation.read or user/*.read—make it possible to enforce least-privilege access. Identity proofing, authentication, MFA, and session management can be handled by enterprise IAM or CIAM platforms.
The final component is the launch and context framework. SMART defines how apps are launched from inside an EHR or launched independently, and how patient or encounter context is passed securely. This eliminates guesswork for app developers and ensures clinicians see relevant information immediately, without navigating or searching manually.
Together, these layers create a complete, unified system that makes SMART on FHIR one of the most powerful interoperability models in healthcare.
Why SMART on FHIR Matters for Security & Identity
Security and identity management are essential in healthcare, and SMART on FHIR is designed with both in mind. Because it is built on OAuth 2.0 and OpenID Connect, SMART ensures that only authenticated, authorized users and applications can access sensitive health data.
Each access token reflects the user’s identity, permissions, and the specific FHIR resources they’re allowed to read or modify. This mapping between identity and access scope is central to modern healthcare compliance.
From an IAM standpoint, SMART on FHIR fits naturally into identity ecosystems where strong authentication, MFA, passwordless access, or biometric verification already exist. CIAM platforms like LoginRadius can unify patient identity, clinician identity, and consumer app access into a single authorization framework. Once a user is authenticated, the identity platform issues an OIDC token that the SMART layer uses to generate FHIR-scoped access.
By integrating identity, access control, consent, and audit logs into the flow, SMART on FHIR helps organizations meet strict regulatory frameworks such as HIPAA, GDPR, and CMS interoperability rules. This tight coupling of health data and identity is one of the reasons SMART has become a preferred model in modern healthcare architectures.
How Developers Build SMART on FHIR Apps
Developing SMART on FHIR apps involves a predictable pattern that makes the process easier than building one-off integrations. Developers register their app with the SMART authorization server, define redirect URIs, and request appropriate SMART scopes.
They then implement the OAuth authorization code flow, handle token responses, and integrate with the FHIR protocol using secure HTTP requests.
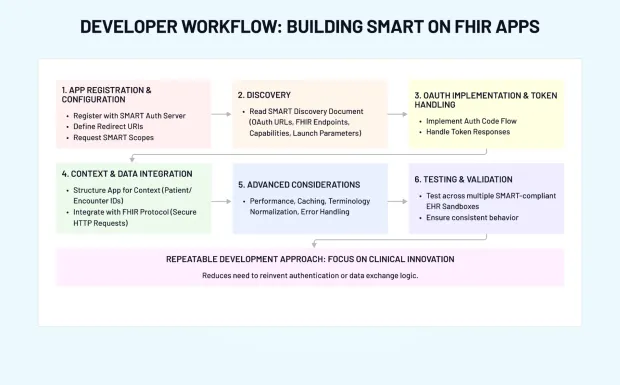
A key step is reading the server’s SMART discovery document, which reveals everything the app needs to operate—OAuth URLs, FHIR endpoints, supported capabilities, and required launch parameters. Developers then structure their app to receive context such as patient or encounter IDs, ensuring the app opens with relevant data in a clinical setting.
Beyond authentication, developers must also consider performance, caching, terminology normalization, and error handling. Since SMART on FHIR apps read live clinical data, the user experience must accommodate different data availability patterns and formats. Testing across multiple SMART-compliant EHR sandboxes ensures the app behaves consistently regardless of deployment site.
This repeatable development approach is what makes SMART on FHIR so attractive. It allows teams to focus on clinical innovation instead of reinventing authentication or data exchange logic.
Building a SMART on FHIR app typically follows these steps:
-
Register your application with the EHR system
-
Configure OAuth 2.0 client credentials
-
Request authorization from the user (patient or provider)
-
Receive an access token from the authorization server
-
Use the token to access FHIR APIs securely
-
Retrieve and display healthcare data within your app
This workflow ensures that all access is secure, standardized, and compliant with healthcare regulations.
Use Cases and Benefits of SMART on FHIR
SMART on FHIR unlocks a wide range of real-world use cases. Clinicians benefit from decision-support tools embedded directly within their workflow, reducing manual chart review and improving diagnostic accuracy.
Patients gain mobile apps that consolidate data across providers, improving engagement and continuity of care. Public health agencies and researchers access standardized data models through the FHIR protocol, supporting cohort analysis, case surveillance, and population health insights.
On the organizational side, SMART on FHIR reduces the need for custom interfaces, resulting in shorter development cycles, lower integration costs, and smoother onboarding for new tools. Because SMART uses modern web standards, it improves security and compliance without forcing teams to rely on dated infrastructure.
Ultimately, SMART on FHIR enhances interoperability by turning EHR data into a secure, open, and accessible resource that supports a vibrant ecosystem of reusable apps.
Real-World Examples of SMART on FHIR in Action
SMART on FHIR is already widely adopted across healthcare ecosystems.
Epic App Marketplace
Epic supports SMART on FHIR apps through its App Orchard, enabling third-party developers to build apps that integrate directly into clinical workflows.
Cerner (Oracle Health)
Cerner uses SMART on FHIR APIs to enable interoperability between healthcare providers, apps, and patient-facing tools.
Apple Health Records
Apple leverages SMART on FHIR to allow users to securely access and aggregate their health records from multiple providers into a single interface.
CMS Interoperability Rule (2020)
The Centers for Medicare & Medicaid Services mandated FHIR-based APIs, accelerating SMART on FHIR adoption across healthcare systems.
These examples demonstrate how SMART on FHIR is becoming the standard for secure healthcare interoperability.
Challenges
Even with its strengths, SMART on FHIR introduces several practical and architectural challenges—especially for organizations transitioning from legacy systems or heterogeneous EHR environments.
Teams must be fluent in FHIR resource modeling, understand the nuances of OAuth 2.0 and OpenID Connect flows, and navigate the complexity of assigning SMART scopes to clinical roles. Data quality is another recurring issue: even when systems use the FHIR protocol, clinical codes, vocabularies, and resource completeness can differ widely. This inconsistency often forces teams to invest in data normalization, terminology mapping, and semantic validation.
Regulated environments add further layers of responsibility. Organizations must ensure that governance controls, consent frameworks, access logging, and audit trails are implemented with precision. Any misalignment can introduce compliance risks, especially when PHI moves between multiple SMART on FHIR apps and services.
Moreover, user adoption challenges—particularly among clinicians already burdened with overloaded workflows—must be addressed early to avoid resistance to new digital tools.
Best Practices for SMART on FHIR Success
To overcome these challenges, organizations benefit from adopting a staged, strategic approach. Starting with focused pilot applications—such as a clinician-facing decision support tool or a patient-facing medication tracker—helps refine implementation patterns without overwhelming the team. This allows identity, FHIR, and app teams to validate workflows, confirm scope permissions, and refine how context is passed before broad rollout.
A mature, compliant FHIR server is non-negotiable. Ensuring the server adheres strictly to SMART on FHIR specifications reduces fragmentation and prevents custom, one-off integrations from creeping into the architecture. Teams should document and centrally manage scope definitions, align access policies with clinical roles, and test authorization flows continuously.
Clinician engagement is critical. Bringing clinicians into the design and validation phases ensures that SMART on FHIR apps actually support real-world workflows, reduce cognitive burden, and enhance usability. Their feedback is essential to shaping workflows that feel intuitive rather than disruptive. Combined with clear communication and training, this increases adoption and generates valuable insights that guide iterative improvements.
When these best practices are followed, SMART on FHIR evolves from a technical integration to a scalable, secure, and clinically meaningful interoperability strategy—one that can support long-term digital transformation across the healthcare system.
Enhancing SMART on FHIR Deployments with LoginRadius CIAM
Identity is the backbone of SMART on FHIR. While SMART defines how apps authenticate, authorize, and receive context, organizations still need a robust identity layer to ensure that the right users get the right access at the right time. This is where a CIAM platform like LoginRadius strengthens the entire architecture.
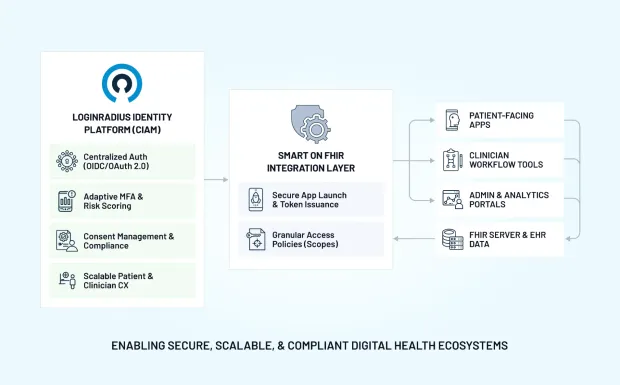
1. Centralized Authentication Across Clinicians, Patients & Admins
LoginRadius offers unified identity management across all user types—patients, clinicians, caregivers, administrators—ensuring consistent, secure login experiences for every SMART on FHIR app. A single identity layer simplifies user management while supporting multi-tenant healthcare environments.
2. Secure OAuth 2.0 & OpenID Connect Foundation
SMART on FHIR depends on OAuth and OIDC. LoginRadius acts as a highly scalable, standards-compliant identity provider that issues OIDC tokens, enforces MFA, supports passwordless login, and integrates seamlessly into SMART authorization flows.
3. Granular Access Policies and Adaptive MFA
LoginRadius allows organizations to enforce role-based access tied to SMART scopes. Adaptive MFA, risk scoring, and device intelligence help ensure that sensitive PHI is accessed appropriately without adding friction to clinical workflows.
4. Consent Management & Compliance Readiness
LoginRadius’ built-in consent tracking and audit trails make it easier to align SMART on FHIR workflows with regulatory obligations such as HIPAA, GDPR, and CMS interoperability rules. This reduces operational and legal risk.
5. Scalable Identity Experience for Patient-Facing SMART Apps
Patient-facing SMART on FHIR apps benefit from LoginRadius’ capabilities like progressive profiling, passwordless flows, social login, and account recovery—all essential for reducing patient login friction.
6. Streamlined Integration with SMART App Launch
Because LoginRadius can serve as the OIDC identity provider, it integrates smoothly with SMART’s app-launch flows, making it easier to authenticate users, issue tokens, and manage sessions across multiple FHIR resources and apps.
By pairing SMART on FHIR with a modern CIAM platform like LoginRadius, healthcare organizations enhance security, streamline onboarding, ensure compliance, and deliver consistent, scalable access experiences across their entire digital ecosystem.
Build Secure SMART on FHIR Apps with LoginRadius
SMART on FHIR requires robust identity, authentication, and consent management.
LoginRadius helps you:
-
Implement OAuth 2.0 and OpenID Connect flows
-
Secure patient and provider identities
-
Enable adaptive MFA for healthcare apps
-
Manage consent and access control at scale
Explore how LoginRadius supports healthcare identity Secure patient identities, enable interoperability, and stay HIPAA-compliant with enterprise-grade CIAM.
Conclusion
As healthcare continues to move toward open, data-driven ecosystems, SMART on FHIR provides the common language that lets innovators safely plug into EHR data. By standardizing data models, authorization flows, and clinical context it gives developers a repeatable pattern and gives organizations confidence that every app request is authenticated, authorized, and auditable.
Pairing SMART on FHIR with a CIAM platform like LoginRadius extends that foundation with centralized identity, adaptive MFA, and consent management at scale. Together, they turn interoperability from a compliance checkbox into a strategic advantage—powering secure, patient-centric digital experiences across the healthcare continuum today and in the future.
FAQs
1. What is SMART on FHIR?
SMART on FHIR is a standard that combines FHIR technology with OAuth 2.0 security to allow apps to securely access healthcare data from EHR systems.
2. What are SMART on FHIR apps?
They are applications built using SMART standards that can securely read and write FHIR data across different hospital systems without custom integrations.
3. How does the FHIR protocol support SMART on FHIR?
The FHIR protocol provides the data model and API structure, while the SMART layer provides authentication, authorization, and context.
4. Why is identity important for SMART on FHIR?
SMART relies on OAuth and OpenID Connect, so secure authentication and user identity directly determine what data an app can access.
Q: How to build a SMART on FHIR app?
A: Developers use FHIR APIs along with OAuth 2.0 authorization flows to securely access EHR data and build interoperable applications.
Q: What are SMART on FHIR scopes?
A: Scopes define the level of access an application has to patient data, such as read or write permissions.
Q: Is SMART on FHIR HIPAA compliant?
A: SMART on FHIR can support HIPAA compliance when implemented with proper security controls like encryption, access control, and audit logging.



