Introduction
Let’s be honest, logging into things isn’t anyone’s favorite part of the day. Whether it’s an app at work, a bank portal, or your cloud dashboard, we all want one thing: quick, seamless access. But here’s the catch: speed can’t come at the cost of security.
The average internet user today juggles dozens of accounts, and most still rely on a single password to protect them. It is convenient, but it is also like putting a flimsy lock on a vault full of gold. In a world where phishing kits are a click away and credential leaks happen by the minute, relying on just a password is a ticking time bomb.
And the consequences are real. A single compromised login of your user can lead to data breaches, ransomware, and reputational damage that takes years to undo. That’s why authentication has moved from being a simple login step to a critical layer of digital defense. But here’s where it gets tricky: the world of authentication is full of jargon — 2FA, MFA, 1FA, biometrics, tokens, push alerts, and it’s easy to get lost in them.
If you’ve ever asked yourself: “What’s the actual difference between 2fa and mfa?”, “Is MFA worth the extra friction for my users?”, “How effective is 2 factor authentication?”, “Do I even need anything beyond a password?”, …then you’re in the right place.
This blog walks through how single-factor authentication (1FA), two-factor authentication (2FA), and multi-factor authentication (MFA) work, when to use them, and what makes them different. You will also encounter real-world examples, security comparisons, and a straightforward framework to select the ideal authentication method for your application or business.
No fluff. No fear-mongering. Just practical, well-explained guidance so you can make smarter decisions about how your users log in and how your data stays safe.
Let’s get into it.
What Is Single-Factor Authentication (1FA)?
Before security tokens, fingerprint scans, or face ID became mainstream, there was a much simpler method of logging in—a good old-fashioned password. That’s the essence of single-factor authentication, often referred to as 1FA or one-factor authentication.
At its core, 1FA means you’re proving who you are using just one thing, usually something you know, like a password or PIN. It’s been the default for decades, and most of us are still using it daily, whether it’s unlocking a phone, accessing Wi-Fi, or signing into a local admin panel.
How Does Single Factor Authentication Work?
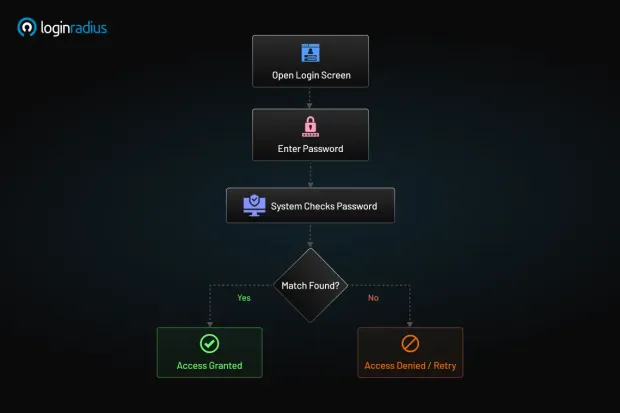
The process is simple:
-
You open a login screen.
-
You enter a credential—let’s say, your password.
-
The system checks that password against a stored value.
-
If it matches, you're in.
That's it. No codes. No secondary device. No additional checks. Just a single layer of verification stands between you and everything on the other side of that screen.
And while this sounds straightforward, the simplicity is both its strength and biggest weakness.
Think of 1FA like using a single key to your house. If someone finds or duplicates that key, they have full access. They don’t need to break in or bypass an alarm system. And in the digital world, “finding the key” could be as easy as buying a leaked password list or crafting a convincing phishing email.
The Limitations of One-Factor Authentication
Passwords are fragile. Here's why:
-
We reuse them. Let’s be honest, who hasn’t used the same password across a few sites?
-
We choose weak ones. “123456,” “password,” and “qwerty” still make the top ten every year.
-
We get tricked. Phishing emails and fake login pages are getting more sophisticated by the day.
-
They get leaked. Major breaches regularly expose millions of password hashes, often just one cracked password away from disaster.
In environments where convenience outweighs risk, single-factor authentication might still fly, like logging into a demo app or a read-only analytics dashboard. But if you’re handling personal data, payment details, intellectual property, or anything remotely sensitive? 1FA isn’t enough anymore.
Why Is Single Factor Authentication Still Used?
Despite its flaws, 1FA is still everywhere. Why?
-
It’s easy to implement. A simple password check is fast and low-cost.
-
It’s familiar. Users understand it—there’s no learning curve.
-
It reduces friction. There’s no waiting for OTPs or pulling out a second device.
But convenience shouldn't be confused with safety. More and more, security-conscious teams are recognizing that while single-factor authentication might check the usability box, it doesn’t check the security one. And when breaches happen, it’s not just data on the line, it’s your reputation.
So while 1FA might still have its place in low-risk scenarios, it’s no longer the standard for serious security. It’s the baseline, and in today’s world, the baseline is just not enough. Even if you rely on using this method, it’s best to enforce your users into choosing a strong password.
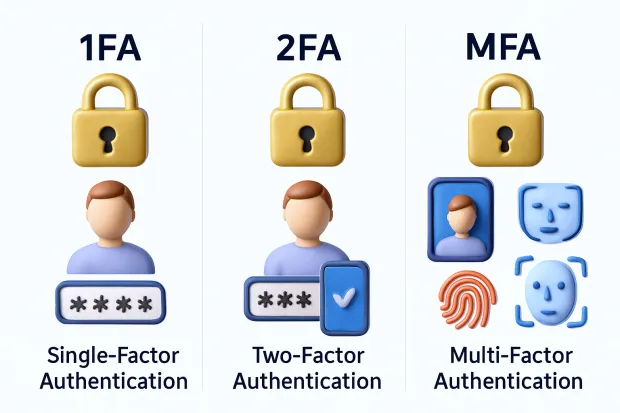
What is Two-Factor Authentication (2FA)?
Let’s say your house key gets stolen. Bad news, right? But imagine if, before someone could open your door, they also had to scan your fingerprint.
Suddenly, just having the key isn’t enough. That’s what two-factor authentication (2FA) is like in the digital world.
Two-factor authentication (2FA) adds an extra layer of security to your digital accounts. It combines two different types of identity verification, making it much harder for attackers to break in even if they’ve already snagged your password.
So, instead of relying solely on “something you know,” like a password, 2FA requires a second element, typically “something you have” (like your phone) or “something you are” (like your fingerprint). It’s a simple concept, but a powerful upgrade in security.
How Does 2FA Work?
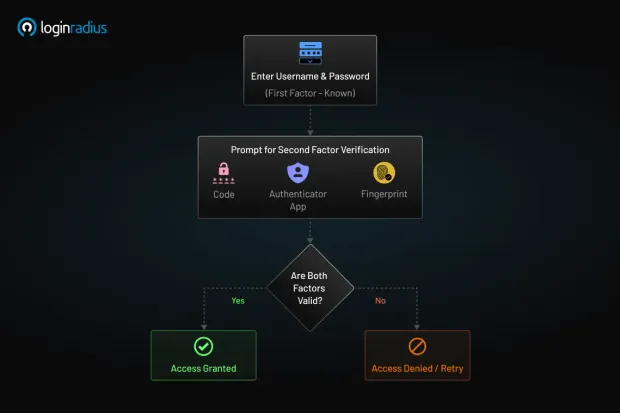
Here’s what happens behind the scenes with two-factor authentication:
-
You enter your username and password, the first factor (something you know).
-
You’re then prompted to verify using a second factor, like a code sent to your phone, a prompt in an authenticator app, or a fingerprint scan.
-
Only after both steps are verified you are granted access.
So even if a hacker has your password, they’re stuck at the second gate. You can read the 2FA guide to learn more about its functionality and implementation.
What Is an Example of Two-Factor Authentication?
You’ve likely already used 2FA without even realizing it. Here are some real-world examples:
-
Logging into Gmail from a new device? You’ll be asked to enter a code sent to your phone.
-
Accessing your work VPN? You might need your password and a one-time code from an app like Google Authenticator.
-
Logging into your bank account? You enter your credentials, then get a push notification to approve the login.
These combinations—password + code, PIN + biometric scan, username + security token are all examples of two-factor authentication.
How Effective Is Two-Factor Authentication?
Now for the important question: How effective is 2FA, really? According to Microsoft, enabling two-factor authentication (2FA) can stop over 99.9% of automated attacks. That’s because most cyberattacks rely on stolen credentials. However, if an attacker doesn’t have access to your second factor, such as your phone, face, or hardware key, they can’t gain entry.
Even if your password is leaked in a breach or guessed through brute force, 2FA acts as a second layer of protection, stopping intruders in their tracks.
Of course, no security measure is 100% bulletproof. There are sophisticated phishing attacks that can bypass certain 2FA methods (especially SMS-based ones), but it’s still a massive step up from password-only systems.
Security Insight: According to Microsoft, accounts using two-factor authentication (2FA) block over 99.9% of automated attacks. However, SMS-based 2FA remains vulnerable to SIM-swapping and phishing, which is why many enterprises now prefer app-based TOTP or hardware-based MFA solutions.
Common 2FA Authentication Methods
Not all second factors are created equal. Here are the most common types of 2FA authentication methods:
One-Time Passwords (OTPs)
-
OTPs are sent via SMS, email, or generated in an app like Google Authenticator or Authy.
-
Time-based, single-use codes that expire after 30–60 seconds.
-
Widely used, but SMS OTPs are susceptible to SIM swapping.
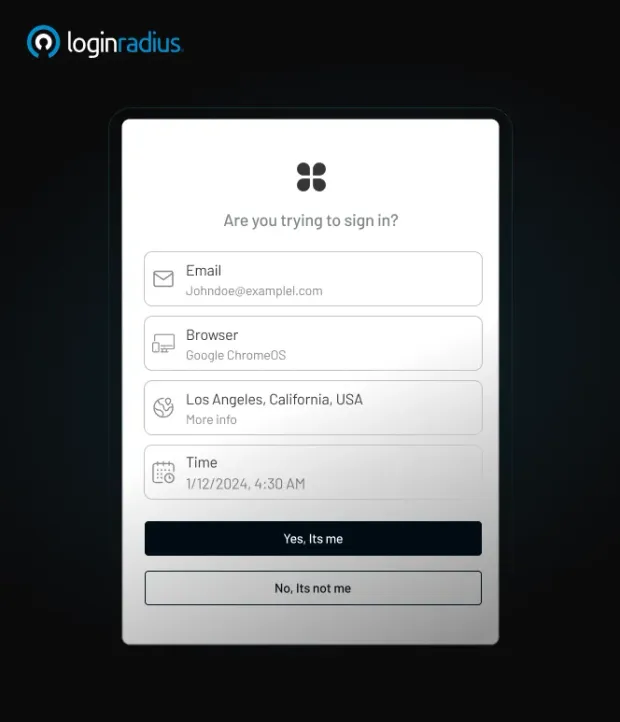
Push Notifications
-
Push notification authentication sends a prompt on your device asking if you’re trying to log in.
-
With one tap, you approve or deny the request.
-
Faster and generally safer than SMS.
Biometric Factors
-
Biometric authentication includes Face ID, fingerprints, or voice recognition.
-
Offers a smooth experience but depends on device compatibility.
Hardware Tokens
-
Physical devices like YubiKey or RSA tokens.
-
Plug into your device or use NFC to authenticate.
-
Very secure, though it may require additional hardware management.
Backup Codes
-
Static, pre-generated codes are used as a fallback method.
-
Not ideal as a primary second factor, but helpful for account recovery.
Each method comes with its pros and cons. For instance, email OTPs are better than nothing, but TOTP apps and hardware tokens offer a stronger line of defense.
Why 2FA Is a Modern Security Baseline
If you take away just one thing from this section, it’s this: 2FA is no longer optional. It’s the new baseline for digital security, especially for applications that handle personal data, payments, or any type of sensitive access.
It’s also the first step toward adopting multi-factor authentication (MFA), which takes things even further. However, for most organizations today, two-factor authentication is the best bang for the buck upgrade you can make to protect your users and your systems.
What Is Multi-Factor Authentication (MFA)?
If two-factor authentication is like locking your door with a key and checking a security camera before opening it, multi-factor authentication (MFA) takes it a step further. It’s like having a guard at the gate, an alarm system, and a fingerprint scanner inside your house. It’s layered security, designed for a world where cyberattacks are persistent and sophisticated.
MFA doesn’t just stop at two pieces of evidence. It uses two or more independent credentials to verify a person’s identity before granting access. These credentials come from at least two different categories of authentication factors:
-
Something you know – A password, a PIN, an answer to a security question.
-
Something you have – A smartphone, a hardware token, an access card.
-
Something you are – A fingerprint, facial recognition, retina scan, or behavioral traits.
Unlike 2FA, which always involves exactly two of these factors, MFA can involve three or more, depending on the level of risk, the sensitivity of the data, and the context of the login attempt.
And in an era where credentials can be bought, sold, and phished within seconds, that extra layer or layers can make all the difference.
How Does MFA Work?
Let’s walk through a real-world MFA scenario to make it tangible. Say you’re trying to access your company’s internal dashboard from a new location.

Here’s what happens:
-
You enter your username and password – something you know.
-
A push notification is sent to your phone – something you have.
-
You confirm the login with a fingerprint scan on your mobile app – something you are.
Only after all three steps are verified will the system let you in.
Behind the scenes, MFA systems also evaluate context, like your IP address, device type, location, or time of day. If something looks off—say you’re logging in from a new device in another country, adaptive MFA might step in and require even more proof, such as a security question or a time-sensitive backup code.
MFA is no longer just a sequence of steps. It’s becoming dynamic and intelligent, adjusting its strictness based on risk signals and user behavior patterns.
Why MFA Is More Than Just "2FA Plus One"
It’s easy to think of MFA as just “2FA with extra steps,” but that undersells its value.
Here’s the difference:
-
2FA is rigid: two authentication steps, always the same.
-
MFA is flexible, consisting of two or more steps, is customizable, and can be conditional.
MFA gives organizations more control. You can build policies that:
-
Require additional factors only for high-risk users or actions
-
Skip MFA for trusted devices
-
Step up authentication only when behavior deviates from the norm
This flexibility is particularly useful for enterprises and applications that handle sensitive data, require remote access, or involve privileged user roles.
So, when people ask about multi-factor vs. two-factor authentication or MFA vs. two-factor authentication, the answer isn't just about the number of steps. It's about control, context, and customization.
MFA in the Real World
Multi-factor authentication isn’t just a security concept on paper; it’s a practice that businesses across various industries use daily to protect their users, platforms, and data.
Here are a few real-world examples of MFA in action:
-
Financial Services: A customer logs in to their banking app using a password and then confirms their identity with a biometric scan or one-time password (OTP). Transactions above a certain threshold might trigger step-up authentication with additional verification.
-
Developer Portals and SaaS Dashboards: Dev teams use SSO credentials, followed by hardware security keys or authenticator app approval, especially when accessing admin-level controls or sensitive APIs.
-
Healthcare Platforms: Doctors and staff access patient records using smartcards and facial recognition, ensuring compliance with privacy regulations like HIPAA.
-
Insurance and Risk Intelligence: Take C-Quence, a modern UK-based insurance provider, for example. They needed a robust authentication solution that could secure their digital platform without compromising user experience.
With LoginRadius, they implemented multi-factor authentication to protect their broker portal, providing users with secure, role-based access and seamless logins. The platform now combines email-based login with one-time passwords (OTPs) and contextual security rules, reducing fraud risks while keeping user workflows friction-free.
These examples prove that MFA is more than just an IT checklist item—it’s a practical and powerful security layer that organizations can tailor to their unique risk profile, user base, and compliance needs.
When Is MFA the Right Choice?
MFA might sound complex, and yes, it does involve some setup, but the protection it offers is well worth the investment. Here’s when MFA becomes a no-brainer:
-
You’re managing a platform with sensitive customer data
-
Your users include remote employees, third-party vendors, or high-risk roles
-
You’re required to meet compliance standards like SOC 2, HIPAA, GDPR, or PCI-DSS
-
You’re offering self-service tools, portals, or APIs to external partners
MFA ensures that even if one factor is compromised, your data stays protected. That’s why it’s considered the gold standard in authentication today.
And with solutions like LoginRadius, you don’t have to build MFA from scratch. You can integrate it using pre-built workflows, APIs, and adaptive policies tailored to your application’s unique needs.
Multi-Factor Authentication vs Two-Factor Authentication: Why It Matters
On paper, two-factor authentication (2FA) and multi-factor authentication (MFA) sound incredibly similar. Both involve more than one method of proving a user’s identity. Both drastically improve security over using passwords alone. So, does it really matter which one you choose?
Actually, yes, it matters more than most people realize.
The key difference between 2fa vs mfa isn’t just in the number of steps. It’s in the degree of flexibility, control, and risk adaptation you get with MFA that makes it stand out. While 2FA always uses exactly two factors (and usually follows a fixed path), MFA opens the door to dynamic combinations of factors, tailored to your use case, user type, or level of threat.
Let’s put it this way:
-
2FA is like installing a second lock on your door. It’s a significant security upgrade—and a great place to start.
-
MFA is like installing a second lock, plus motion sensors, an alarm system, and a smart doorbell that only activates when someone is approaching.
You’re not just adding more steps, you’re adding more intelligence to your security.
Here’s why this distinction matters:
1. Scalability Across Use Cases
With 2FA, every user gets the same path. MFA, on the other hand, allows different access flows based on user type, access level, or sensitivity of action. For example, you could require stricter verification for an admin changing billing info, and a simpler flow for a user updating their profile picture.
2. Context Awareness
MFA systems can analyze context, like login location, device fingerprint, and time of day, and trigger different authentication flows accordingly. That’s something traditional 2FA doesn’t do.
3. Regulatory Compliance and Risk Mitigation
Certain industries, such as finance and healthcare, require more than just basic 2FA. MFA allows you to meet these standards without reinventing the wheel.
4. Better Security Hygiene
As cyber threats evolve, MFA allows businesses to adapt authentication policies without ripping and replacing systems. Need to add biometric verification or behavior-based risk scoring? MFA makes it possible, without requiring you to rebuild your entire flow.
How to Choose the Correct Authentication Method for Your Company
Quick Checklist: Which Authentication Method Should You Use?
| Ask Yourself This… | If Yes → Consider This Method |
|---|---|
| Are your systems low-risk and internal-only? | ✅ 1FA may be sufficient |
| Do you manage customer data or support remote logins? | ✅ 2FA is a strong starting point |
| Are you in a regulated industry (e.g., finance, health)? | ✅ Go for MFA with adaptive policies |
| Do users need flexible login flows with low friction? | ✅ Choose MFA with step-up capability |
| Do you support vendors, partners, or privileged access? | ✅ MFA with contextual enforcement |
So, which Authentication Method should you go with?
Two-factor authentication (2FA) is ideal for organizations starting their security journey. It’s simple to implement, widely understood by users, and offers excellent protection against basic threats.
MFA is the right fit for organizations that handle sensitive data, high-risk transactions, or a diverse range of user types. If you’re thinking long-term and want flexible, adaptive, and intelligent authentication, multi-factor authentication (MFA) is your answer.
And yes, every 2FA setup is technically a form of MFA, but in practice, not all MFA is limited to two steps. The real power of multi-factor authentication lies in its ability to evolve with your needs.
Choosing the correct authentication method for your company ultimately depends on risk levels, compliance needs, user experience goals, and available technology resources.
Platforms like LoginRadius simplify this choice by offering plug-and-play support for 2FA and advanced MFA flows—including SMS, OTPs, biometric integrations, and adaptive step-up authentication.
Conclusion
Authentication has come a long way. What used to be a simple password field is now one of the most critical components of any secure digital system. As cyberattacks become bolder, smarter, and more frequent, our approach to identity verification must keep pace.
Ultimately, it’s not about adding more security tools to your login flow. It’s about choosing the right approach for your users, your systems, and your data. If you’re a growing company seeking to implement robust security without compromising the user experience, two-factor authentication (2FA) may be your best starting point.
But if you’re managing large volumes of user identities, sensitive customer data, or complex B2B workflows, then investing in MFA is a smart move for both your reputation and your resilience.
Still unsure which authentication method best suits your needs?
LoginRadius makes it easy to implement both 2FA and MFA with flexible options like OTPs, biometric verification, adaptive policies, and developer-friendly APIs. Contact us today to see how we can help you build smarter, safer, and more scalable login experiences.
FAQs
What is an example of two-factor authentication?
A common example is logging in with your password (something you know) and then entering a one-time code sent to your phone (something you have). This double-check adds an extra layer of security.
What is the difference between single-factor and multi-factor authentication?
Single-factor authentication uses only one method to verify identity, usually a password. Multi-factor authentication uses two or more methods from different categories to enhance security.
How many types of MFA are there?
MFA typically involves three types: something you know (e.g., a password), something you have (e.g., a phone or token), and something you are (e.g., a fingerprint or facial recognition).
What are the disadvantages of single-factor authentication?
It's highly vulnerable to breaches, as stolen or weak passwords are easy targets. Without a second layer of defense, attackers can gain full access with just one compromised credential.