Ecommerce is booming! Market analysts say that global ecommerce will touch a whopping $7.4 trillion by 2025. And it is expected to grow even further in coming years, as consumers now have endless options at their fingertips. They can easily get whatever they want, within no time, from the comfort of their homes.
But for the ecommerce businesses, this fiercely competitive market is nothing short of a sea of challenges. Consider this: a staggering 70% of online shopping carts are abandoned due to complex checkout journeys.
Plus, your customers expect your website and app to be in perfect sync. And when everyone's trying to buy during a big sale, your site shouldn’t crumble under the pressure.
Moreover, the cost of acquiring a single new customer can easily climb to $45 or more, putting immense pressure on marketing budgets. On top of that, you must keep the fraudsters out! That's a constant battle that cost businesses over $41 billion worldwide.
So, how to tackle these ecommerce challenges? We will discuss all that and more, in this blog! We'll delve into the core issues and, more importantly, provide actionable solutions to help you not just survive, but flourish in today's dynamic ecommerce landscape. So, let’s get started!
The Key Ecommerce Challenges
Every ecommerce business is unique. They might cater to different sets of consumers, and provide different sets of benefits. BUT, more than 90% of them nowadays face these key ecommerce challenges:
-
Cart Abandonment & Checkout Friction
-
Lack of Customer Insight & Personalization
-
The Omnichannel Experience Gap
-
Scaling for Peak Performance
-
The Ever-Present Threat of Fraud & Cyberattacks
-
Navigating Compliance & Legal Complexities
Let’s dive deeper into these challenges and see how we can solve them.
1. Cart Abandonment & Checkout Friction
Imagine "Sarah," a potential customer, excited about the new smart home device she just added to her cart. She proceeds to checkout, only to be met with a “mandatory” account creation. She now has to pass through endless form fields asking for her personal information, including some she's already provided before.
Her excitement dwindles with each extra click, and suddenly, that "must-have" item isn't worth the hassle. She hits the back button, and your potential sale vanishes into the digital ether.
Well, that Sarah can be literally anyone in today’s ecommerce landscape! Studies show that a complicated checkout process is a top reason for abandonment (22%). Mandatory account creation alone drives 26% of abandonments. And this lost conversion doesn't just mean a missed sale; it means wasted marketing spend on customer acquisition and a potentially lost loyal customer.

The Solution
So here’s what you can do to improve your customer’s checkout experience, and potentially your sales conversions:
-
Offer Guest Checkout & Streamlined Login: Don't force registration. Allow customers to complete their purchase quickly. For returning users, enable social login options (like Google, Facebook, Apple). You can also try single sign-on (SSO) and passkeys across your digital properties.
-
Minimize Form Fields & Leverage Progressive Profiling: Collect Only What’s Necessary - Let the Data Grow with the Relationship. With progressive profiling, you gather essential user information at the point of need—starting with minimal data to reduce friction during sign-up or login. Over time, as trust builds, you can request additional details through strategically timed interactions. Modern CIAM solutions like LoginRadius support this approach by enabling features like autofill, smart address validation, and seamless data enrichment, ensuring a personalized experience without overwhelming users upfront.
-
Transparent Pricing Upfront: Hidden costs for shipping or taxes are a major turn-off. Display all charges clearly and early in the process. 48% of shopping carts are abandoned due to unexpected extra costs (SellersCommerce).
-
Diverse & Preferred Payment Options: Support popular digital wallets (e.g., Apple Pay, Google Pay), Buy Now Pay Later (BNPL) services, and a wide range of credit/debit cards. The more options, the less friction.
-
Optimize for Mobile: With over 75% of retail website visits and 67% of online orders coming from smartphones (DesignRush), a mobile-first, responsive checkout experience is non-negotiable.
-
Implement Abandoned Cart Recovery: Automated email or SMS sequences can gently remind customers of their pending purchase and offer incentives like discounts or free shipping to bring them back.
By prioritizing a frictionless checkout powered by seamless identity management, you can significantly boost conversions, reduce lost sales, and turn frustrated shoppers into loyal customers.
2. Lack of Customer Insight & Personalization
In a digital world overflowing with choices, customers don't just want products. They crave experiences tailored just for them! Consider this: 90% of US consumers find personalization appealing (Statista).
And failing in it actually leads to losing revenues. As studies by McKinsey indicate that personalized experiences can uplift revenue by 10-15%.
Yet, for many ecommerce businesses, understanding who their customers truly are, what they want, and how they behave across different touchpoints remains a profound mystery.
The core issue often stems from relying solely on transactional data, which only tells you what was purchased, when, and for how much.
This approach creates a significant blind spot. It doesn't reveal why customers bought that. What their deeper preferences are. How they interact with your brand across channels, or their potential long-term value.
The Solution
To move beyond just guessing and truly unlock the power of personalization, online businesses need to focus on gaining comprehensive customer insight. Here's how:
Build a Unified Customer Profile
Break down those internal data silos. Gather all customer information – from website visits and purchase history to app usage, customer service interactions, and email engagement – into a single, comprehensive profile.
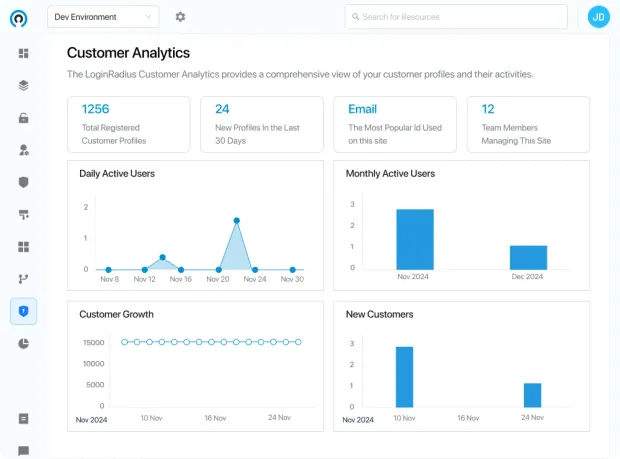
A robust Customer Identity and Access Management (CIAM)solution can act as this central hub, consolidating diverse customer attributes and behaviors into one accessible identity that goes far beyond just what they've bought. Look how easy it is to get valuable insights from the LoginRadius console:
Track Behavior for Deeper Insights
Implement tools to actively monitor customer journeys. This includes understanding their click paths, which products they view, and where they might abandon their session. Knowing how customers interact helps you identify their intent and spot any friction points in their user experience.
Power Personalization with AI
Leverage Artificial Intelligence and machine learning to analyze your unified customer data. This allows you to deliver dynamic, real-time recommendations for products, content, and offers. It's about moving beyond simple "customers who bought this also bought..." to truly one-to-one personalization that makes a real difference.
Segment Your Audience Smartly
Go beyond basic demographics. Create detailed segments of your customer base based on their purchase behavior, engagement level, preferences, and their current lifecycle stage. This intelligent segmentation enables highly targeted marketing campaigns that resonate.
Collect Preferences Directly (and Ethically)
Ask customers about their preferences during sign-up or profile updates. This consent-driven approach ensures you're gathering valuable insights ethically and remaining compliant with data privacy regulations.
A modern CIAM platform can help you securely collect and manage these preferences, enriching customer profiles in a user friendly way.
Connect Customer Journeys Across Channels
It's essential that your customers are recognized as the same individual, whether they're logging in from their laptop, mobile app, or interacting via social media.
This seamless recognition, which a CIAM solution is designed to manage, is foundational for delivering a truly consistent and personalized omnichannel experience that drives customer satisfaction.
By gaining deeper customer insights and enabling effective personalization, you can transform anonymous visitors into valued individuals, build stronger relationships, increase conversion rates, and significantly boost customer lifetime value.
3. The Omnichannel Experience Gap
In today's digital age, your customers don't stick to a single channel. They might browse products on your mobile app during their commute, add items to their cart on their laptop at home. Then visit your physical store to see an item in person. And finally, reach out to customer service via social media!
This is the omnichannel experience in action. The problem arises when these touchpoints feel disconnected, creating jarring experiences. Nearly 80% of customers prefer an omnichannel experience. Hence, making all these interactions feel like one smooth, continuous journey is a significant challenge for online businesses.
When your online store, app, physical location (if applicable), and social media presence don't "talk" to each other, it leads to friction and frustration. Imagine a customer starting a support chat on your website, explaining their issue, and then needing to call your support line, only to have to repeat their entire story because their previous interaction isn't visible.
This kind of disjointed experience erodes trust and can lead to lost sales and decreased customer satisfaction. In fact, companies with strong omnichannel engagement strategies retain an average of 89% of their customers. While those with weaker strategies retain only about 33%. This massive gap in retention directly impacts customer lifetime value (CLTV) and overall revenue.
The Solution
Bridging the omnichannel experience gap requires a strategic approach to integrate all customer touchpoints into a unified whole. It can be done in the following ways:
Implement a Unified Customer View
Just like understanding customer insight, the foundation here is a single view of your customer across all channels. This means integrating data from your website, app, CRM, POS, and customer service platforms.
A comprehensive Customer Identity and Access Management (CIAM) solution is crucial here. It acts as the central identity layer that connects all customer interactions and ensures a consistent identity regardless of the channel used. This central identity management for retail ensures no data is siloed.
Ensure Consistent Branding and Messaging
From your online store's look and feel to your social media voice and in-store promotions, ensure absolute consistency. This prevents customer confusion and reinforces your brand identity.
Enable Cross-Channel Functionality
Allow customers to start a task on one channel and finish it on another. This could include "Buy Online, Pick Up In-Store" (BOPIS) options, which are gaining immense popularity. It is estimated that $154.3 billion in US sales by 2025 for click-and-collect options. You can also enable returns of online purchases in physical stores.
Personalize Across All Touchpoints
With a unified customer view, you can extend personalization beyond just your website. Tailor emails, app notifications, and even in-store interactions based on a customer's known preferences and behaviors across all channels. This enhances the overall user experience.
Train Staff for Omnichannel
Ensure your customer service and sales teams are equipped with the tools and training to access customer history and provide consistent support, regardless of the channel the customer uses to reach out. This is vital for reducing customer frustration and improving customer satisfaction.
Leverage Identity for Seamless Transitions
A robust CIAM platform facilitates single sign-on (SSO) across all your digital properties (website, app, loyalty program), making transitions between channels smooth and frictionless for the customer. This greatly enhances the user experience and reinforces a truly unified brand interaction.
By meticulously building a cohesive omnichannel experience, you not only meet evolving customer expectations but also foster stronger loyalty, increase retention, and drive significant revenue growth across all your sales channels. Unlock the secrets to engaging customers in the omnichannel world — get your free eBook now:
4. Scaling for Peak Performance
For any online business, major sales events like Black Friday, Cyber Monday, or seasonal promotions are prime opportunities for massive revenue spikes. But these periods also present a critical challenge: can your digital infrastructure handle the sudden, immense surge in traffic and transactions without faltering?
The pressure is immense. A mere one-second delay in page load time can result in a 7% reduction in conversions. And 40% of users will abandon a website that takes more than three seconds to load. Even more critically, an average of $5,600 per minute is the estimated cost of downtime for large enterprises, translating to hundreds of thousands of dollars per hour.
This scenario doesn't just mean immediate lost sales. It leads to frustrated customers, negative reviews, and a damaged brand reputation that can take years to rebuild.
The Solution
To truly scale for peak performance and turn high-traffic periods into revenue successes, ecommerce businesses must invest in robust and agile infrastructure solutions. It can be done as follows:
Cloud-Based Scalability
Migrate to cloud hosting platforms (e.g., AWS, Azure, Google Cloud) that offer auto-scaling capabilities. This allows your infrastructure to automatically adjust resources (servers, bandwidth) up or down based on real-time traffic demands, ensuring consistent performance without manual intervention.
Content Delivery Networks (CDNs)
Implement a CDN to distribute your website's static content (images, videos, CSS, JavaScript) across servers globally. This reduces latency by delivering content from a server geographically closer to the user, significantly improving loading speeds and user experience, especially during high traffic.
Implement Robust Identity Management
User authentication and identity management for retail can become a bottleneck during traffic spikes if not handled efficiently. A scalable Customer Identity and Access Management (CIAM) platform is designed to handle millions of simultaneous login requests, ensuring that your authentication systems do not become the weak link in your performance chain. This maintains a smooth user experience even when your customer base is surging.
5. The Ever-Present Threat of Fraud & Cyberattacks
The landscape of cyber threats is incredibly diverse, ranging from sophisticated identity thefts and data breaches that expose sensitive customer information to rampant account takeover (ATO) attacks, where fraudsters hijack legitimate customer accounts.
Bots constantly try to exploit vulnerabilities, leading to fraudulent purchases or inventory manipulation.
For online businesses, this isn't just a distant possibility; it's a daily battle that can lead to devastating financial losses and severe damage to customer trust.
Consider the scale: online payment fraud alone accounted for over $41 billion in global losses in 2022. This number continues to climb every year.
And these attacks don't just result in direct financial loss from chargebacks and stolen goods. They inflict severe reputational damage, erode customer satisfaction, and can lead to costly legal and compliance repercussions.
Customers simply won't return to an online store where their data or accounts feel insecure. Building and maintaining customer trust requires robust security measures.
The Solution
Protecting your online business and customer base from the relentless threat of fraud and cyberattacks demands more than just basic protection. It requires a strategic, multi-layered defense. Here are key security measures online retailers can implement.
Implement Strong Authentication
Move beyond simple passwords. Adopt multi-factor authentication (MFA) for all customer logins. This adds an essential layer of security by requiring a second form of verification (e.g., a code sent to their phone) in addition to their password, making account takeover attempts significantly harder.
Technologies like biometric identity verification for ecommerce (fingerprint, facial recognition) and passkeys are emerging as highly secure and user friendly alternatives.
Leverage Fraud Detection Systems
Utilize AI-powered fraud detection tools that can analyze transactional patterns, device data, and behavioral biometrics in real-time to identify and flag suspicious activities. These systems help reduce the risk of fraudulent transactions before they are completed.
Secure Customer Identity Management
A robust Customer Identity and Access Management (CIAM) solution is a foundational pillar for fraud prevention. It securely manages all customer identities and access credentials, implementing strong encryption, strict access controls, and continuous monitoring.
This centralized approach significantly prevents fraud at the authentication layer by verifying identities and thwarting unauthorized access.
Real-time Monitoring & Incident Response
Establish systems for continuous monitoring of your network and user activity for unusual patterns. Have a clear, well-rehearsed incident response plan to quickly contain and mitigate the impact of any security incidents. A well-defined verification process for suspicious activities is crucial.
Regular Security Audits & Updates
Periodically conduct comprehensive security audits and penetration testing to identify vulnerabilities in your online store's infrastructure, applications, and APIs. Staying updated with the latest security patches and protocols is non-negotiable in protecting against data breaches.
6. Navigating Compliance & Legal Complexities
For online businesses, managing customer data comes with a big responsibility - following an ever-growing list of privacy laws! From Europe's GDPR to California's CCPA, and India's new DPDP Act, these rules are designed to protect customer information.
But keeping up can be tough. If you don't comply, the costs can be huge. GDPR fines alone have topped $4.8 billion (approx. €4.5 billion) since 2018. Beyond fines, a data breach due to poor compliance can seriously harm your reputation and erode customer trust.
Imagine a situation where your online store's customer data collection doesn't meet a new privacy standard. Or, worse, sensitive customer profiles are exposed because your security measures weren't up to code.
These issues can lead to expensive investigations, legal problems, and a big drop in customer satisfaction. For online retailers, understanding and following these rules isn't just about avoiding penalties; it's about building trust with your customer base by showing you value their privacy.
The Solution
Staying ahead of data privacy and legal compliance requires a clear, proactive strategy. This means making compliance a core part of your operations, not an afterthought.
-
Know Your Regulations: Understand which data privacy laws apply to your online business based on where your customers are located. Keep an eye on new laws and updates.
-
Collect Only What's Needed: Only gather the essential data for your operations. Always get clear permission from customers before collecting or using their data. A strong Customer Identity and Access Management (CIAM) solution can help you manage these permissions, letting customers easily control their privacy settings in a user friendly way.
-
Boost Data Security: Put robust security measures in place to protect customer data from data breaches and unauthorized access. This includes encryption and strict access controls. Many compliance laws require specific technical and organizational safeguards, and modern identity management for retail solutions are built with these high standards in mind.
-
Handle Customer Data Requests: Be ready to manage requests from customers who want to access, correct, or delete their personal data (like the "right to be forgotten"). A centralized customer profile powered by a CIAM solution can simplify the verification process and help you handle these requests efficiently.
-
Regularly Check Your Practices: Periodically review how you collect, store, and process data. Conduct assessments to find and reduce the risk of privacy problems before they happen.
-
Choose Compliant Partners: Make sure all third-party vendors and partners you work with (like payment processors or marketing platforms) also meet relevant data privacy laws.
To Sum Up
The ecommerce landscape of 2025 presents significant hurdles, from cart abandonment and customer insight gaps to fraud threats and compliance complexities.
Overcoming these challenges is not just about survival; it's essential for achieving sustainable growth and building a loyal customer base.
Many of the actionable solutions discussed are fundamentally strengthened by effective customer identity management for retail, offering a clear path forward.
And at the heart of many of these solutions lies a crucial element: effective customer identity management for retail. A unified and secure approach to how customers register, log in, and manage their personal data.
Good CIAM solution providers like LoginRadius provide the backbone for improved user experience, enhanced personalization, seamless omnichannel journeys, robust fraud prevention, and simplified compliance. And the best part is, you can get a completely FREE version of LoginRadius for your retail app, that will remain free forever! Try out today.